Main section
What is an information security management system (ISMS)?
Protect your sensitive data and minimise risks: an information security management system (ISMS) provides structured security and helps companies meet legal requirements.
As a Swiss Trust Service Provider that is subject to comprehensive regulations, we explain the objectives and components of a successful ISMS based on our own experience.
Information security management system (ISMS): basics and benefits
An ISMS is typically implemented on the basis of internationally recognised standards such as ISO/IEC 27001, which provide organisations with a structured approach to planning, implementing, monitoring and continuously improving information security. The purpose of an ISMS is to systematically identify, assess and manage information security risks, enabling organisations to increase their resilience to security incidents and maintain continuous operations and service availability. As a Swiss certificate authority, SwissSign has successfully implemented a ISMS for years – verified by an average of 13 audits per year.
The three protection goals of an ISMS: confidentiality, integrity and availability
The main objective of an ISMS is to protect what is known as the ‘CIA triad’ of information security: confidentiality, integrity and availability.
Confidentiality
Ensuring that information can only be viewed, used or processed by authorised individuals, systems or processes. This is achieved through access controls, encryption and strict authentication procedures.
Integrity
Ensuring that information is accurate and complete and cannot be modified or deleted without authorisation. Integrity measures can be supported by mechanisms such as checksums, version control and regular backups.
Availability
Ensuring that information and systems are always accessible to authorised users whenever needed. This requires measures for preventing outages, enabling rapid recovery after outages and ensuring redundancy.
Additionally, an ISMS also aims to establish a high degree of transparency and trust between organisations and their stakeholders (customers, employees, partners, authorities, etc.) by demonstrating that appropriate security measures have been taken to minimise risks.
In SwissSign’s case, these stakeholders not only include shareholders (Swiss Post) and customers (companies and authorities from Switzerland, Germany, Austria and many other countries worldwide), but also supervisory authorities – which monitor compliance with signature regulations such as the eIDAS Regulation and ESigA – and industry organisations such as the CA/Browser Forum, where major browser manufacturers (including Google and Apple) meet with the world’s certificate authorities to establish the rules for secure SSL/TLS and S/MIME certificates.
What purposes does an ISMS serve?
An ISMS is intended to support organisations in effectively protecting their information/data resources while simultaneously meeting business, legal and regulatory requirements. An ISMS is more than just a technical system. It is also a holistic management approach that takes into account technical, organisational and human factors.
Risk management
An ISMS enables organisations to systematically identify, assess and address risks related to their data/information resources. At SwissSign, we simply have to ensure that each person is who they claim to be and be able to protect their data. By applying a risk-based approach, organisations can efficiently deploy their resources to address the most relevant threats.
Compliance with laws and regulations
Many industries and countries have strict information security and data protection regulations. An ISMS helps organisations to meet these requirements by demonstrating a systematic approach to information and data security. For SwissSign, this includes compliance with the European Union’s GDPR and Switzerland’s FADP, as well as requirements set out by the CA/Browser Forum.
Business continuity
A well-implemented ISMS helps to make organisations more resilient to security incidents such as cyber attacks, information/data loss or natural disasters. It supports the development of contingency plans and recovery measures to ensure that operations and service provision can be maintained (as far as possible) even during a crisis (even if only minimally) and enables the fastest possible return to normal operations. For an organisation like SwissSign, which guarantees the security of its customers’ communications, this is absolutely essential for conducting business.
Trust and reputation
An ISMS strengthens the trust that customers, employees, partners and other stakeholders have in an organisation’s ability to protect sensitive information and data. This is particularly important in industries where handling confidential services, information and data plays a pivotal role, such as SwissSign as a Trust Service Provider (TSP), with its digital certificates, electronic signature solutions and digital identity verification services.
Cultural transformation
Implementing an ISMS promotes a security culture within organisations. Through training and awareness programmes, employees are continuously encouraged to become aware of just how important information security principles are and to take appropriate action.
Cost efficiency
An ISMS helps to avoid potential costs associated with security incidents, information and data losses or legal and regulatory sanctions. By taking preventive measures, damage can be detected and reduced early on, cutting costs in the long term.
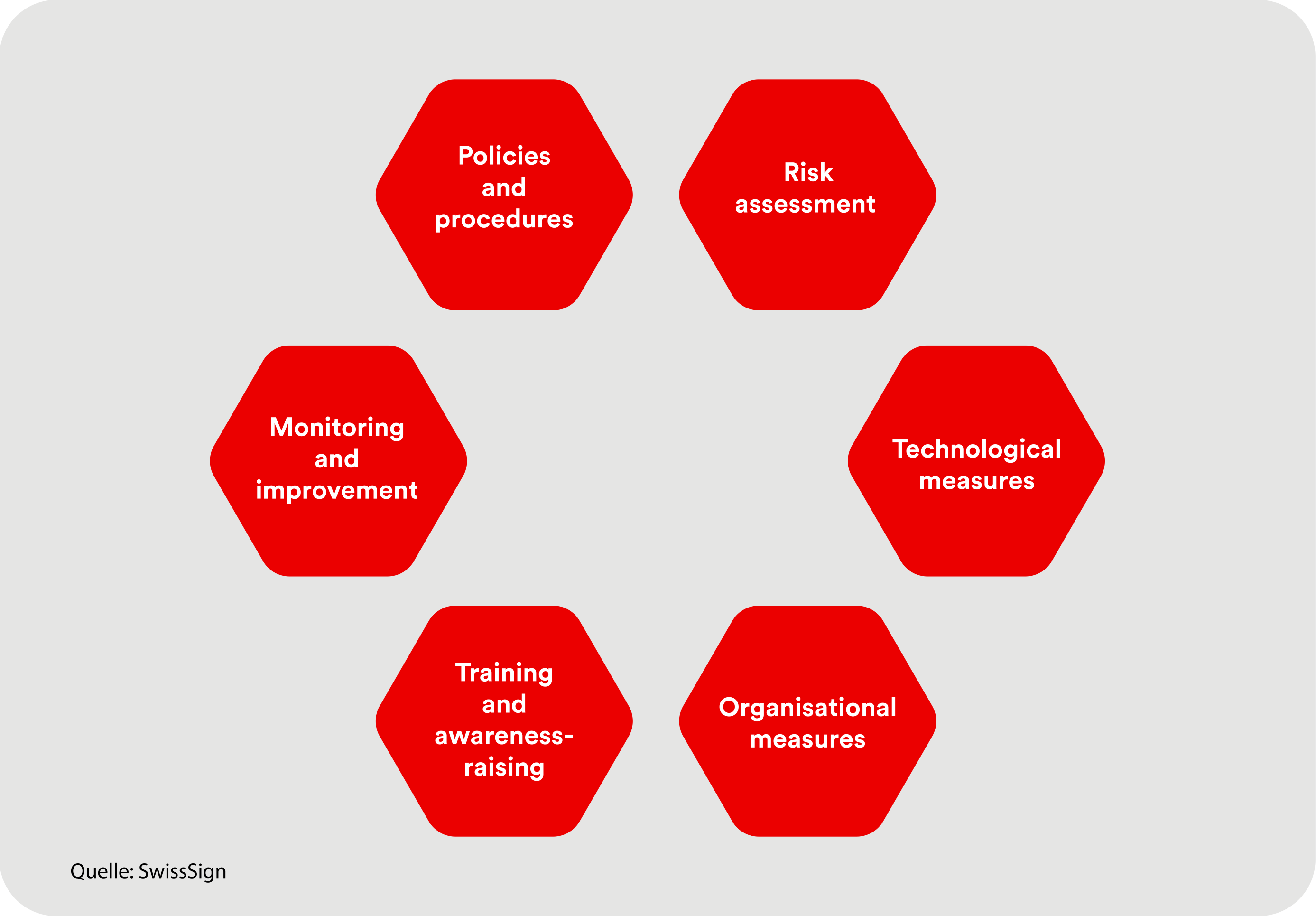
Components of an ISMS
An ISMS comprises several core components that work together to guarantee an organisation’s information security:
-
Policies and procedures: Documented guidelines (policies, procedures, work instructions, etc.) that regulate information and data handling, security requirements and responsibilities within the organisation.
-
Risk assessment: A structured process (operational risk management (ORM) and business impact analysis (BIA)) for identifying and evaluating security risks, including defining risk handling measures.
-
Technological measures: The deployment of security solutions such as firewalls, antivirus programs, encryption technologies and intrusion detection/prevention systems.
-
Organisational measures: Measures such as access and entry controls, security checks and regular security audits.
-
Training and awareness-raising: Programmes that inform employees about threats, established security practices and the role they play in protecting information and data.
-
Monitoring and improvement: Continuously monitoring security measures, conducting audits and implementing improvements based on new risks or technologies.
Implementing an ISMS: the PDCA cycle
The process of implementing an ISMS typically follows a Plan-Do-Check-Act approach (PDCA cycle, also known as the ‘Deming cycle’). This ensures that the system is set up in a systematic way and is continuously being improved:
1. Plan
-
Defining the scope of the ISMS
-
Identifying information and data assets and risks
-
Developing security policies and objectives
2. Do
-
Implementing planned measures
-
Training and raising awareness of employees
-
Implementing security checks
3. Check
-
Conducting audits and security assessments
-
Reviewing measures for their effectiveness
-
Analysing security incidents
4. Act
-
Implementing improvements based on audit results
-
Adapting the ISMS to changed parameters
Challenges and advice when introducing an ISMS
Introducing and implementing an ISMS is not a simple and easy task and can involve various challenges:
-
Resource scarcity: Introducing an ISMS requires financial and staff resources that are not always readily available.
-
Resistance to change: Employees and managers may demonstrate resistance to new processes or additional security measures.
-
Complexity: Integrating an ISMS into existing systems and processes can be complex from a technical and an organisational standpoint.
-
Dynamic threat landscape: The constantly evolving cyber threat landscape requires the ISMS to be continuously adapted and updated.
-
Proof of effectiveness: Organisations must prove that the implemented measures are actually effective, often through certifications such as ISO/IEC 27001.
For smaller companies in particular – SwissSign is also an SME – implementing an ISMS is undoubtedly a significant undertaking.
The necessary resources lay the foundation for absolutely everything. Strategic decision-making and the operational manpower to manage the introduction and audits are vital. However, even a small team can achieve this if its members network with the industry, follow the latest trends and share best practices with other security professionals. Last but not least, they must bring their organisation’s employees along for the ride, as every security culture either sinks or swims with them.
Summary: why an ISMS is absolutely indispensable
An ISMS is an essential tool for ensuring information security in organisations. Not only does it serve to protect sensitive information, but it also helps to ensure business continuity, meet legal requirements and strengthen stakeholder trust – and can thus generate genuine competitive advantages.
By taking a structured approach that takes into account technical, organisational and human aspects, organisations can minimise risks and effectively achieve their security objectives. However, successfully implementing and continuously improving an ISMS requires commitment, resources and a security culture that is embedded throughout the entire organisation. As a Swiss Trust Service Provider, we are proud of the fact that we invest heavily in the security and trustworthiness of both our organisation and our certificates.






